Solana co-founder Anatoly Yakovenko pushed an immutable binary of Percolator on April 23 and publicly invited developers to try to exploit it for rewards, according to a Cointelegraph post citing the deployment. Locking the binary means the code cannot be patched once live, which raises the cost of any missed bug and turns the bounty into a very direct test of Solana's engineering claims.
As of April 23, 2026, SOL trades at $85.83, down 2.2% on the day and up 0.8% on the week, per CoinMarketCap. BTC sits at $78,023 and the Fear & Greed index reads 60, Greed. The price reaction to the Percolator deployment has been muted so far, which tracks with the technical, developer-facing nature of the announcement.
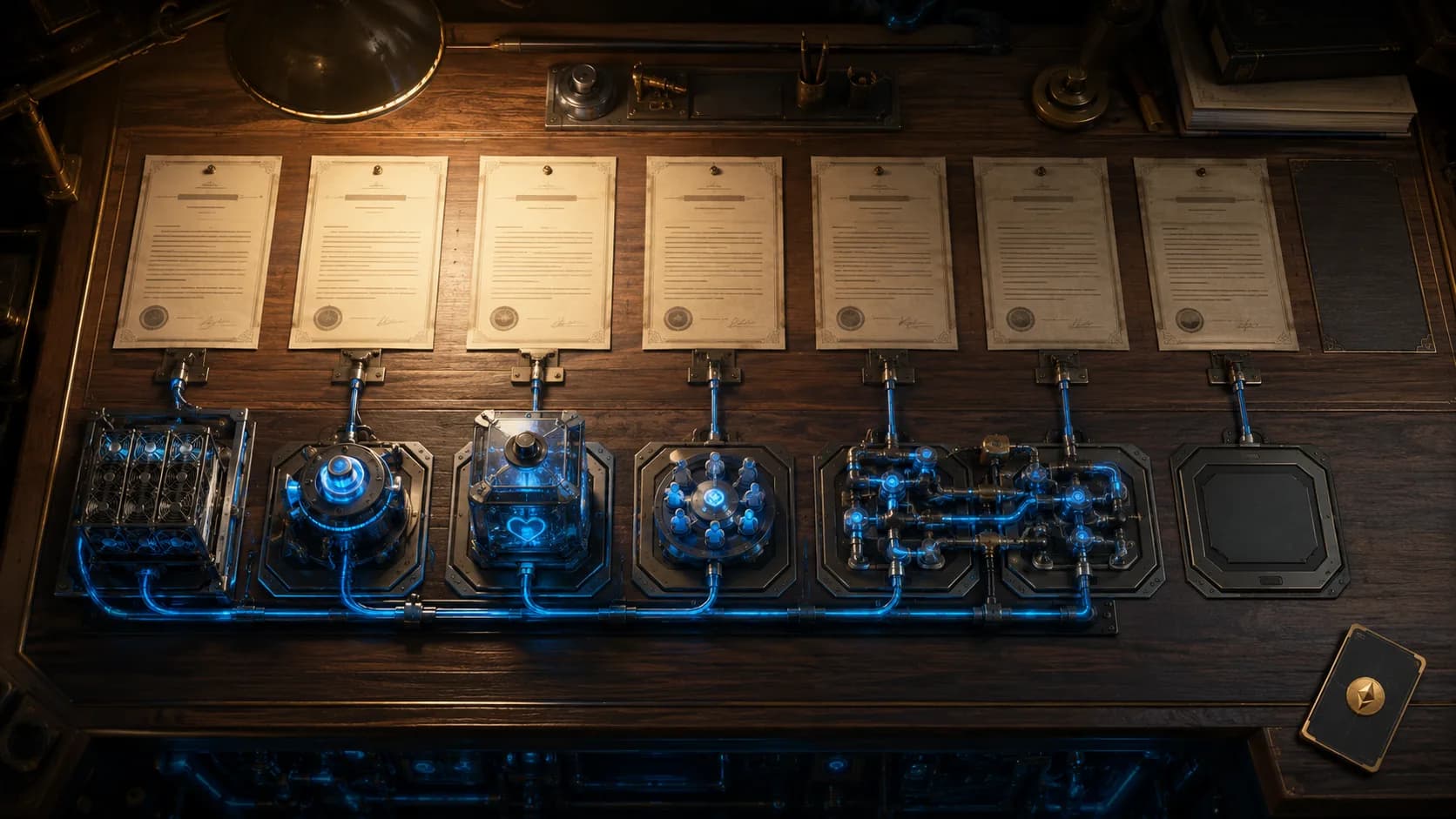
What Percolator Actually Does
Percolator is a transaction scheduling and ordering component that sits inside the Solana validator stack. It decides how incoming transactions are filtered, grouped, and handed off to execution. On a chain that advertises sub-second confirmation and tens of thousands of transactions per second, the scheduler is one of the more sensitive pieces of code in the protocol. A subtle flaw in ordering logic can create MEV opportunities, unfair priority, or in worse cases a denial-of-service path for the validator that runs it.
Shipping an immutable build of that component is a deliberate move. Most critical Solana software ships as mutable binaries that validators can hotfix if something goes wrong. Making Percolator immutable removes that escape hatch.
Why Immutable, and Why Now
Immutability serves two purposes. It forces auditors and attackers to treat the code as the final artifact rather than a moving target, and it commits the team to whatever the binary actually does. Yakovenko has argued for months that Solana's core pieces should be hardened to the point where hotfixes are an embarrassment rather than a routine. Deploying Percolator this way is that argument made concrete.
The bounty framing matters too. Public offers to pay for working exploits do two things at once: they price the worst-case attack and they pull eyes from researchers who would otherwise sell a bug through private channels. The exact bounty size was not detailed in the initial post, so interested researchers will need to check the official Solana bounty program for scope and payout terms before acting on it.
What Could Go Wrong
The downside is obvious. If a researcher finds a real flaw, the only response options are a coordinated chain-level workaround or shipping a new binary that validators must opt into. Neither is clean. A bad enough bug could stall Solana's block production or force validators to run unofficial patches, which is exactly the kind of fragmentation the network spent the last two years trying to leave behind.
Solana has had well-documented outages tied to scheduler and resource management issues. The October 2021 halt, the February 2022 congestion event, and several later restarts all touched the transaction pipeline in some form. A confident, locked deployment of Percolator is a bet that those problems sit in a different part of the stack, or that they have already been fixed.
Signal for Developers Building on Solana
For teams building on Solana, especially DeFi users, market makers, DEXs, and MEV-sensitive applications, the shift has practical consequences. Ordering behavior should now be stable across validator restarts, which makes timing-sensitive code easier to reason about. Any opportunity that relied on quirks of the previous scheduler behavior is likely to stop working, and any assumption that the scheduler will get a quiet tweak next month is off the table.
For wallets and card issuers routing SOL or Solana-based stablecoin payments, the direct impact is small. Payment-grade transactions rarely sit close enough to the ordering edge to notice. A more reliable scheduler is net positive for anyone depending on Solana rails, including spenders using vendors like RedotPay, Jupiter, and Solflare who route transactions through the base layer.
Overview
Yakovenko's immutable Percolator deployment is a confidence signal dressed up as a challenge. Lock the code, put money on the table, let the adversarial process run. If nothing breaks, Solana gets a harder-to-attack scheduler and a cleaner story to tell institutional users. If something does break, the response will be public and expensive, which is exactly what immutability is designed to force.