Axiom's $390M Revenue Machine Has an Access Control Problem
On-chain investigator ZachXBT published his long-anticipated insider trading report on February 26, and the target is Axiom, the Solana-based trading platform that went through Y Combinator's Winter 2025 batch and has generated over $390 million in revenue to date.
The core allegation: multiple Axiom employees exploited the company's internal dashboard, which grants unusually broad access to user data, to look up private wallet addresses and trade on that privileged information. The abuse reportedly dates back to early 2025.
The investigation centers on Broox Bauer, a senior business development employee at Axiom based in New York City, but implicates a wider circle of employees and associates.
What the Internal Dashboard Exposed
According to ZachXBT, Axiom's internal tools gave employees access to a level of user data that is unusual for business development roles. The dashboard reportedly exposed:
- A user's entire wallet list with date and time stamps
- The wallets each user was tracking
- Full transaction history
- Wallet nicknames assigned by the user
- Linked accounts
Any employee with dashboard access could look up any Axiom user by referral code, wallet address, or user ID. In a recorded call obtained during the investigation, Broox stated he could "find out anything to do with that person" using these tools.
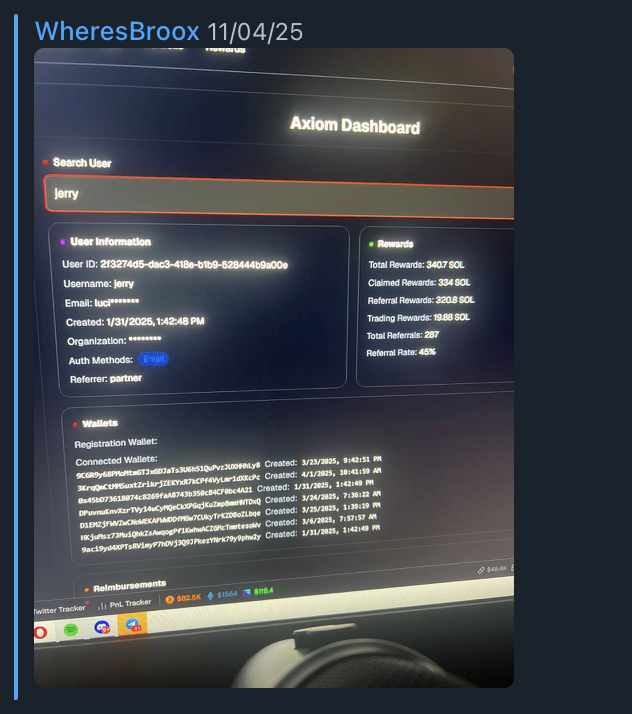
Axiom's internal dashboard as shared by Broox (November 2025). The search for user "Jerry" exposes full wallet lists, registration timestamps, email, organization, referral data, and reward balances. This level of access was available to BD employees. Image via ZachXBT.
This is not a case of a sophisticated hack or a zero-day exploit. It is a case of a profitable company failing to implement basic access controls on sensitive user data.
The Scheme: From Dashboard Lookups to Google Sheets
ZachXBT's investigation, which he was retained to conduct after receiving reports of misconduct, documents a progression of abuse:
April 2025: Broox shared a screenshot from an internal Axiom dashboard displaying private wallets for a trader known as "Jerry."
August 2025: Broox sent a second image showing registration details and connected wallets for another trader, "Monix." In the same month, he discussed lookups of Axiom users who traded the meme coin "AURA."
Ongoing through 2025-2026: The group created a Google Sheet compiling wallet addresses for multiple KOL (Key Opinion Leader) targets, using data obtained from the internal Axiom dashboard by Broox. Multiple KOLs named on the sheet or in leaked screenshots were independently contacted and confirmed the accuracy of the wallet data attributed to them.
Broox described in the recorded call how he researched 10 to 20 wallets initially and slowly increased the number over time "so it does not look that suspicious."
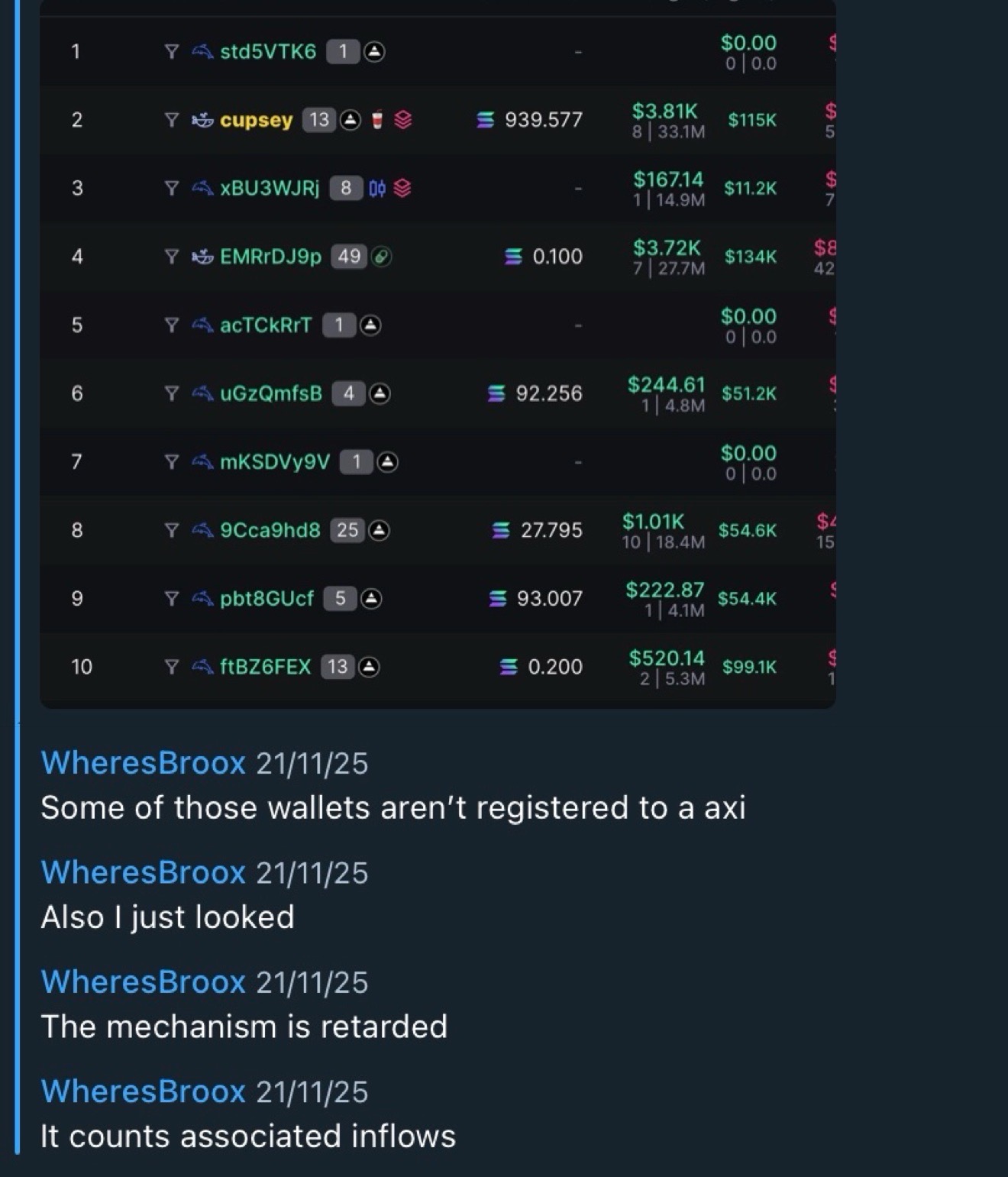
Wallet tracker and Broox messages (November 2025). The list shows tracked wallets with associated PnL data. Broox's messages confirm he was actively looking up wallet registrations through the Axiom dashboard. Image via ZachXBT.
Why KOLs Were the Target
One of the targeted KOLs was a trader known as Marcell, who has a reputation for using followers on X and Telegram as exit liquidity. Marcell was targeted because he bought large portions of token supply for meme coins (a practice known as bundling) from private wallets before promoting them to followers.
Traders like Marcell are prime targets for this type of abuse because address reuse is uncommon and private wallets are rarely public. That makes privileged information from an internal dashboard far more valuable than anything available on-chain. If you know which wallets belong to a KOL who is about to promote a token, you can front-run the pump.
The Wider Circle: At Least Four Employees Named
The recorded call from February 2026 involved more than just Broox. Present was his close friend Gowno (Seb), a recently hired Axiom moderator. But the conversation revealed a wider network.
Broox alleged that Ryan (Ryucio), another Axiom BD employee, had already been using the internal dashboard to look up users on behalf of others. According to Broox, Ryan also helped get his friend Mystery hired at Axiom as a moderator, potentially expanding the circle of people with access to sensitive data. Neither Ryan nor Mystery was present in the recorded call.
During the call, Broox laid out an operational structure. He set ground rules for how Gowno should request wallet lookups from him, offered to send the full compiled list of wallets, and discussed how Gowno's responsibilities at Axiom would grow over time so he could eventually conduct lookups himself. The endgame: Broox outlined a plan to help Gowno profit $200,000 quickly by exploiting the wallet data to front-run KOL trades.
The scheme was already producing returns. Broox shared screenshots of his exchange balances in private chats showing his portfolio growing from $21,170 in July 2025 to $196,161 months later, a 9x increase.
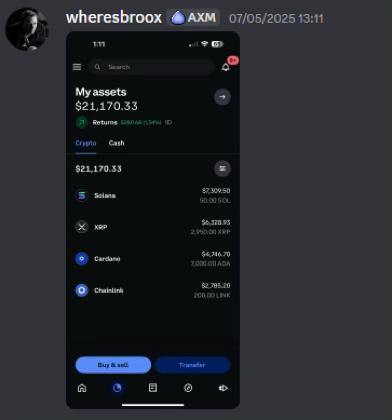
Broox's exchange balance in July 2025: $21,170 across Solana, XRP, Cardano, and Chainlink. Image via ZachXBT.

Broox's exchange balance months later: $196,161, a 9x increase. The screenshot shows 16.6% monthly growth. Image via ZachXBT.
His main wallet was identified via messages sent in a private chat:
FarpaWkzio7WQVpQeu2eURvNQZ3pCBZupJ95wUjoHcUN
Due to the high volume of meme coin trades tied to related addresses, ZachXBT noted that pinpointing high-confidence examples of insider trading from wallet activity alone is difficult without access to Axiom's internal logs to review trade timing. This is a critical distinction: the on-chain evidence shows the money moved, but proving the trades were informed by privileged dashboard data requires Axiom's internal access logs.
Funds from Broox's related addresses primarily flowed to five CEX deposit addresses, suggesting systematic off-ramping of trading profits rather than casual portfolio management.
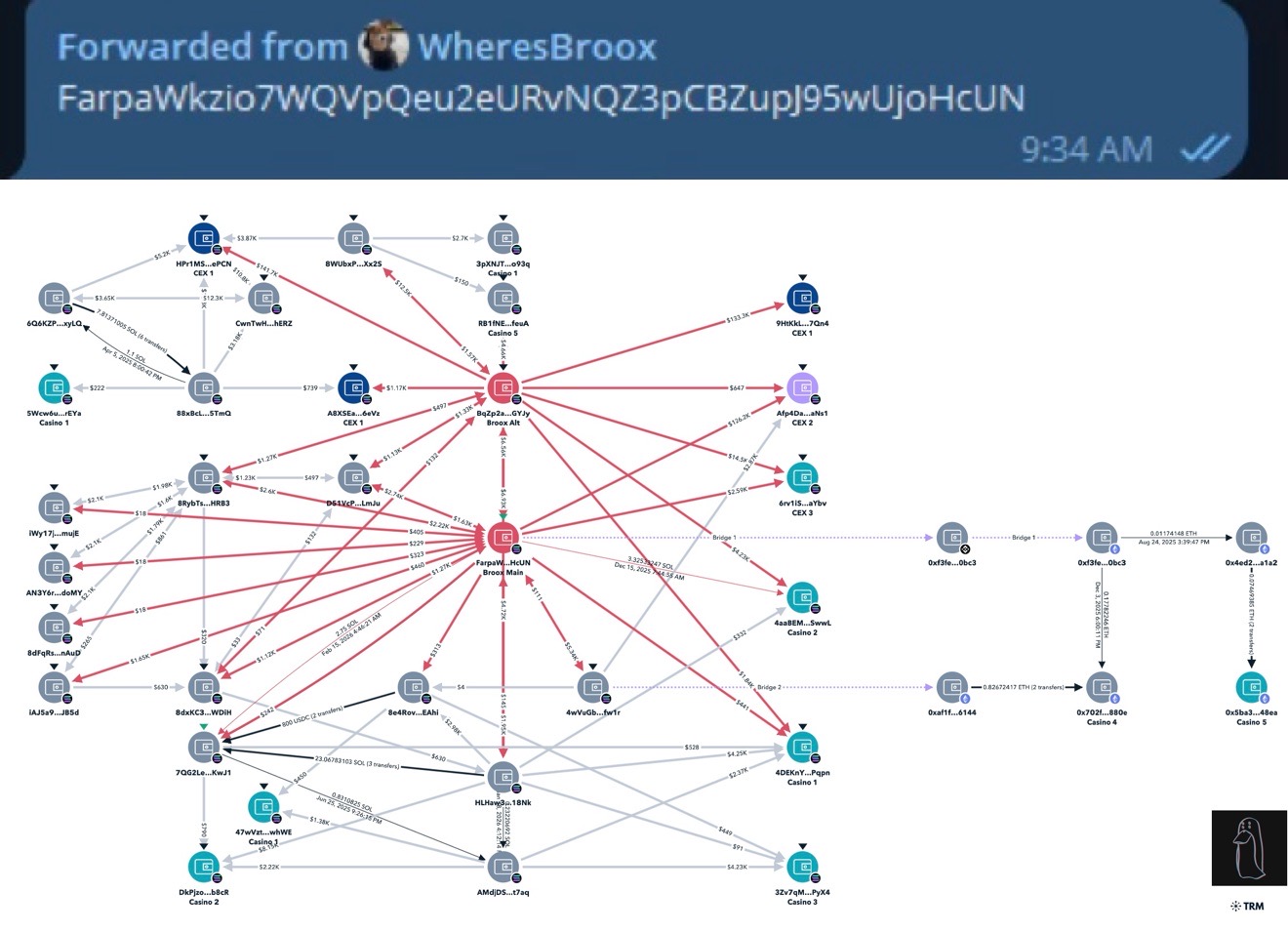
Fund flow analysis of Broox's main wallet (TRM Labs). The graph maps connections from the primary wallet to multiple CEX deposit addresses, casino wallets, bridge transactions across Ethereum, and associated alt wallets. The complexity of the flow network suggests deliberate obfuscation. Image via ZachXBT.
Axiom's Response and the Access Control Question
ZachXBT reached out to the Axiom team for comment before publishing. Axiom provided a statement, which ZachXBT attached to the original thread. The key question now is whether Axiom will take legal action against the employees involved and implement the access controls that should have existed from day one.
Regardless of whether co-founders Cal and Mist were aware of the abuse, ZachXBT's central point stands: there was little to no monitoring or access controls in place to prevent this from happening. No audit logs. No role-based access restrictions. No alerts when an employee runs dozens of user lookups per day.
For context, this is a company that hit $100 million in revenue faster than any startup in Y Combinator's history, according to The Block. It passed $300 million in 263 days. Yet its internal data governance appears to have been an afterthought. A BD employee could search any user by name, ref code, or wallet and see everything: their connected wallets, transaction history, tracked addresses, even the nicknames they gave their wallets. That level of access would raise flags at any fintech company, let alone one processing hundreds of millions in trading volume.
SpendNode's Take: This Is a Governance Problem, Not Just a Rogue Employee
The Axiom case is a textbook example of what happens when a company scales revenue faster than it scales internal controls. Y Combinator's fastest company to $100 million in revenue was also, apparently, a company where a BD employee could look up any user's private wallets from a dashboard with no audit trail.
We think three things here:
First, this is not unique to Axiom. Every centralized trading platform, exchange, and aggregator with user data faces this risk. The difference is whether they have access controls, audit logging, and separation of duties. Axiom apparently did not. How many other fast-growing crypto startups have similar gaps? The answer is probably uncomfortable.
Second, this validates the self-custody thesis. When you use a custodial platform, you are trusting not just the company but every employee with dashboard access. Self-custody crypto cards and non-custodial wallets eliminate this attack vector entirely. Your wallet addresses are still on-chain, but the link between your identity and your wallets stays private.
Third, ZachXBT's suggestion about SDNY jurisdiction is pointed. Broox is based in New York City. The Southern District of New York has been aggressive on crypto enforcement. Whether or not this rises to criminal insider trading charges (the legal bar is high for assets that may not be classified as securities), the pattern of accessing private data to front-run trades is the kind of case regulators have been signaling interest in.
What Crypto Users Should Do Now
If you use Axiom or any trading aggregator:
- Assume your wallet data is visible to platform employees. This is true for every centralized platform, not just Axiom.
- Use separate wallets for trading and holding. Do not connect your main portfolio wallet to trading bots or aggregators.
- Rotate wallets periodically. If you have been using Axiom since 2025, your wallet history is likely in their database.
- Consider self-custody alternatives for holdings you do not need to actively trade. Platforms like Bleap and Tria offer self-custody spending without exposing wallet data to a centralized dashboard.
The $3 Million Prediction Market That Called It
Before ZachXBT named anyone, the crypto community was already placing bets. A Polymarket prediction market on which company would be exposed drew $3 million in volume, with Axiom as the leading candidate at 32% odds. Meteora trailed at 21%, followed by Pump.fun and Jupiter. At least one trader netted $39K betting correctly on Axiom before the report dropped.
The fact that prediction markets correctly identified the target days before publication raises its own questions. ZachXBT himself acknowledged a possible leak as speculation peaked. The irony of an insider trading investigation being front-run by prediction market bettors was not lost on crypto Twitter.
Overview
ZachXBT's February 26 investigation reveals that multiple Axiom employees allegedly abused internal dashboard access to look up private user wallet addresses and insider trade since early 2025. Senior BD employee Broox Bauer is the central figure, with evidence including recorded calls, internal dashboard screenshots, and a Google Sheet of KOL wallet targets. The case exposes a fundamental access control failure at one of crypto's fastest-growing platforms, with $390 million in revenue but apparently no monitoring of employee data access. The investigation raises broader questions about user data security across all centralized trading platforms.