Vitalik Buterin posted at 08:05 UTC on April 18, 2026 that eth.limo, one of the most widely used gateways for resolving Ethereum Name Service (ENS) addresses on the public web, has been hit by an attack on its DNS registrar. The eth.limo team contacted him directly about the incident, and Buterin relayed the warning so users would know to treat the service with caution while the team responds.
As of the time of writing, the eth.limo team has not yet published a full technical postmortem, and the exact scope of the attack, including whether DNS records were actively tampered with or only targeted, is not yet public. Buterin's post is the primary source for the incident at press time.
The eth.limo Role in ENS Resolution
eth.limo is a bridge between the Ethereum Name Service and standard web browsers. ENS lets users register human-readable names like vitalik.eth on-chain, but most browsers do not natively resolve .eth addresses. eth.limo solves that by letting someone type vitalik.eth.limo into a browser and get routed to the content that ENS name points to, whether that is a personal page, a wallet address view, or decentralized storage content.
The service has been a common fallback for ENS users for years because it works without installing a browser extension and without running an Ethereum node locally. That convenience also concentrates trust in one place. If eth.limo's routing is manipulated at the DNS level, anyone using the gateway could be sent somewhere they did not expect.
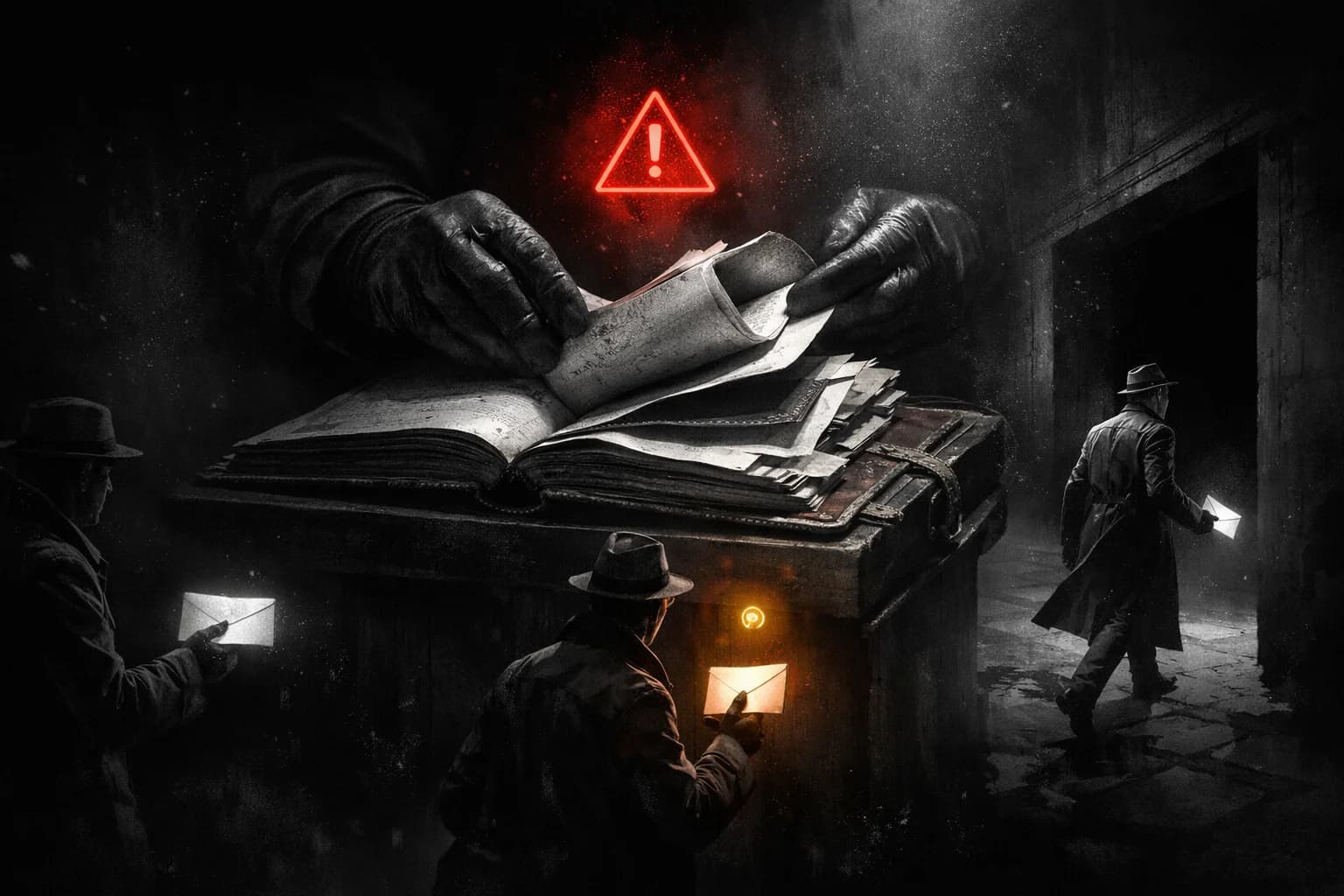
How a DNS Registrar Hijack Redirects Users
A DNS registrar attack usually means an attacker gains access to the account or credentials that control a domain's DNS settings at the registrar level. From there, they can change the authoritative nameservers, rewrite A or CNAME records, or point a subdomain at a different server entirely.
For a service like eth.limo, the effect is dangerous because the user still sees the correct URL in their browser bar. The domain is real. The routing underneath it is not. A visitor checking what address their ENS name resolves to could, in theory, be shown a forged value. A wallet connection prompt could be served from a malicious origin dressed up to look like the real one.
Buterin did not confirm which specific records were touched, or whether the attacker was able to serve modified content before the team intervened. The team disclosed the issue itself, which generally indicates either a detected anomaly at the registrar or confirmed unauthorized access to registrar controls.
Why ENS Users Should Take Action Right Now
The safest step for anyone relying on eth.limo during an active incident is to stop using it until the team publishes an all-clear update. Alternatives include running a local resolver that handles ENS directly, using a wallet that resolves ENS on-chain without going through a web gateway, or using a different gateway that has not been affected.
Users who approved transactions or signed messages on a page loaded through eth.limo in the hours around the attack window should review wallet activity and consider rotating approvals for any contract that could move funds on their behalf. If a gateway was ever serving altered content, signed approvals against the wrong contract address are the most likely way for funds to leak out.
A quick checklist for the next 24 hours:
- Pause any eth.limo tabs and clear cached .eth.limo pages.
- Resolve .eth names through your wallet or an alternative path where possible.
- Revoke any suspicious token approvals via a revocation tool.
- Wait for the eth.limo team's own postmortem before resuming use.
Web2 Dependencies Still Sit Under Web3 Frontends
The incident is a reminder that a lot of what users think of as on-chain still travels over regular internet infrastructure. DNS, TLS certificates, and hosting providers sit between the Ethereum protocol and the browser. ENS names are settled on Ethereum, but last-mile resolution for users who are not running their own node runs through services that can be attacked the same way any other domain can.
In recent years, several crypto frontends have been hit by DNS hijacks or registrar compromises where the on-chain contracts were untouched but the web interfaces were redirected long enough to phish approvals from users. The fix in each case was a combination of restoring DNS records, adding registrar-lock protections, and in some cases moving to registrars with stricter account security. A gateway like eth.limo carries this class of risk on behalf of many users at once, which is why even a short routing incident can have outsized impact.
For users who want less dependence on any one web gateway, the concrete step is to configure a wallet or browser to resolve .eth directly. MetaMask, Brave, and Opera have native ENS resolution for some content types, and self-hosted resolvers are available for power users. Those paths skip the gateway entirely and skip the risk that a registrar attack on any single domain can redirect traffic. Users who prefer broader self-custody options usually pair wallet-native resolution with hardware signing, which adds a second check before any approval goes on-chain.
Overview
Vitalik Buterin confirmed an active DNS registrar attack on eth.limo, a widely used ENS gateway, on April 18, 2026. The attack affects DNS-level routing, not the Ethereum protocol or ENS contracts themselves, but it can still redirect users to unintended destinations if they access ENS content through the gateway. Users should pause use of the service until the team publishes an update and, where possible, resolve .eth names directly through a wallet or local resolver. Anyone who signed messages or approved transactions via eth.limo during the incident window should review and revoke suspicious approvals now rather than wait for the postmortem.