On This Page
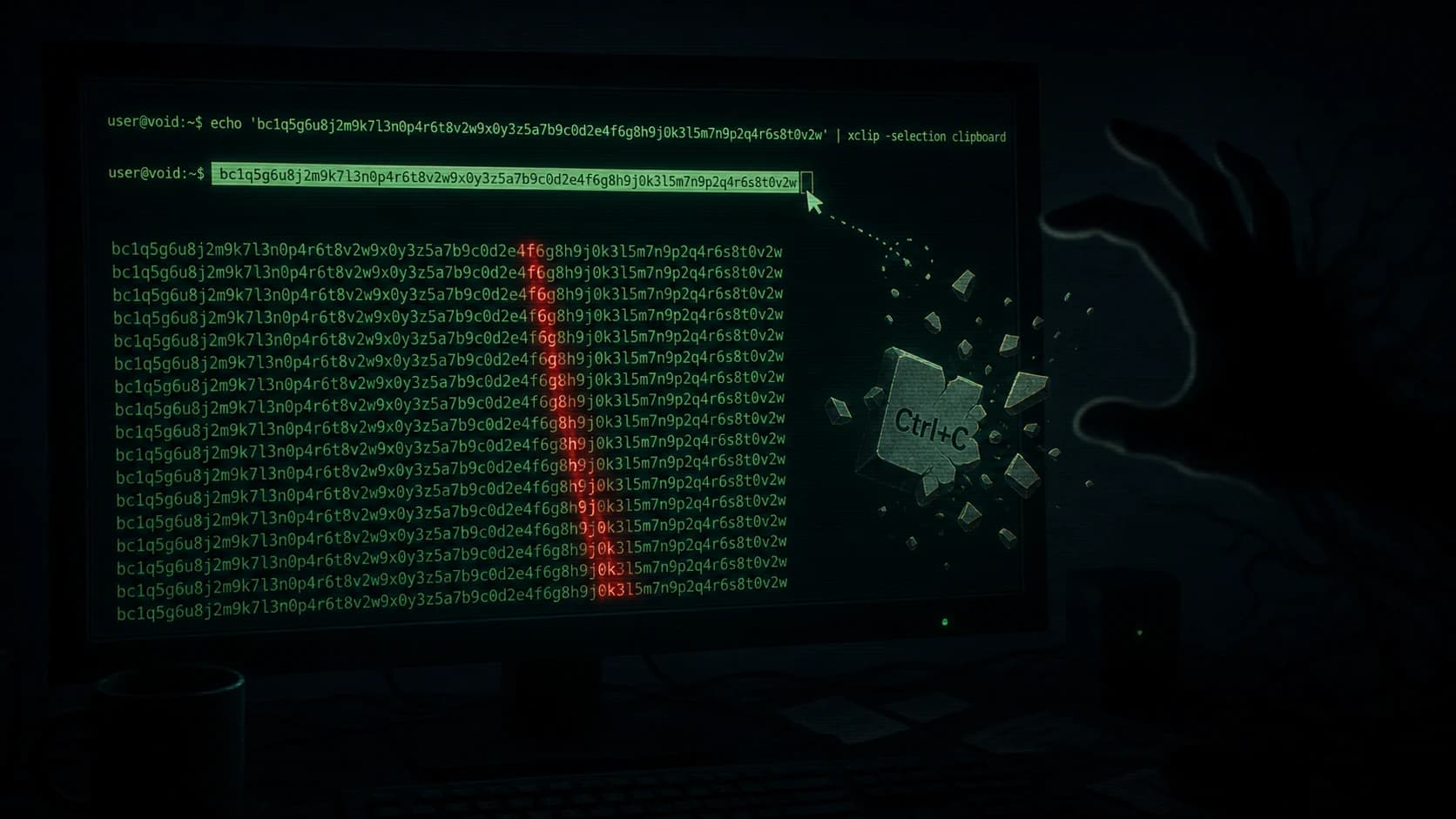
Cointelegraph published a warning on May 2, 2026, that a newly reported Linux flaw, branded "Copy Fail" by researcher Xint Code, allows attackers to interfere with copy operations on affected systems. The outlet framed the disclosure bluntly: "Linux is compromised." Full technical details from Xint Code were still being circulated at the time of writing, but the reported behavior alone is enough to put crypto users on alert.
The market context matters less than the operational one. As of May 2, 2026, BTC sits at $78,425 (-0.0% on the day), ETH at $2,307 (-0.1%), and the Fear & Greed index reads 45 (Neutral). Quiet markets are exactly the windows in which security incidents do the most damage, because attention is elsewhere.
Why a clipboard-class flaw is unusually dangerous for crypto
Clipboard data is the silent backbone of self-custody. Every withdrawal from an exchange, every interaction with a hardware wallet companion app, every test transaction to a fresh address depends on a copy-paste step. If a privileged or unprivileged process can observe or rewrite that buffer, the attacker does not need to break cryptography. They only need the user to paste.
Clipboard hijacking is one of the oldest known techniques against crypto holders. Malware families dating back to 2017 already shipped with regex matchers tuned to BTC, ETH, TRX, and SOL address formats, swapping a freshly copied destination for an attacker-controlled one a few characters before the user clicked Send. The pattern works because most people glance at the first and last four characters and trust the middle.
A bug at the Linux system layer raises the ceiling of that attack from "user installed a bad package" to "user is on a vulnerable distribution." That is a meaningful jump.
What Cointelegraph and Xint Code described
The public framing so far is narrow: a "Copy Fail" condition affecting how Linux handles a copy operation, with Xint Code positioned as the originating researcher. Cointelegraph did not publish a CVE identifier in the headline post and did not name specific distributions or kernel versions in the snippet circulated on X. Crypto users should treat the report as a developing disclosure: real enough to act on, not yet detailed enough to triage by patch level.
If you maintain validators, run a self-hosted node, or use a Linux laptop as your primary signing environment, the safe assumption today is that any cross-process copy on that machine could be observed or modified by a local attacker. Behave accordingly until the upstream patch lands.
Practical steps for crypto users on Linux right now
A few habits raise the cost of this attack class significantly, regardless of how the Copy Fail disclosure ultimately resolves.
First, never paste a destination address straight into a wallet UI without verifying the full string. Read the first six and last six characters out loud against the source. Address-swap malware is tuned for the exact opposite: a quick visual glance at the prefix and suffix.
Second, prefer hardware wallets that display the full destination on their own screen and require physical confirmation. A Ledger or comparable device is checking the address on hardware the host OS cannot tamper with. Users weighing self-custody options can review self-custody crypto cards that integrate with hardware signers.
Third, keep signing environments minimal. A dedicated Linux machine that does nothing but hold keys and sign transactions is far less exposed than a daily driver running browser extensions, package managers, and game launchers.
Fourth, monitor official distribution security trackers. Debian, Ubuntu, Fedora, and Arch all publish per-package advisories. When a CVE is assigned to the Copy Fail report, the patch landing in your distribution is the moment the operational risk drops back to baseline.
How this fits the broader 2026 security trend
Crypto security incidents this year have increasingly originated outside protocol code. The Aave rsETH episode in April, the Wasabi Protocol deployer-key compromise, and the dormant Ethereum wallet drains all involved infrastructure or operational failures rather than smart-contract logic. A clipboard-layer bug at the OS level fits the same pattern: the cryptography held, the human and the host did not.
The right response is not panic. It is consistency. Verify destinations, sign on hardware, segment your environments, and update on schedule. None of these defenses depend on the specifics of the Copy Fail bug holding up under further analysis.
Overview
Cointelegraph reported on May 2, 2026, that researcher Xint Code disclosed a Linux "Copy Fail" bug that can interfere with copy operations on affected systems. Crypto users on Linux are particularly exposed because clipboard hijacking is a well-established attack vector against wallet workflows. Until distribution patches and a CVE arrive, treat any cross-process copy as untrusted, verify pasted addresses in full, and sign on hardware where possible.