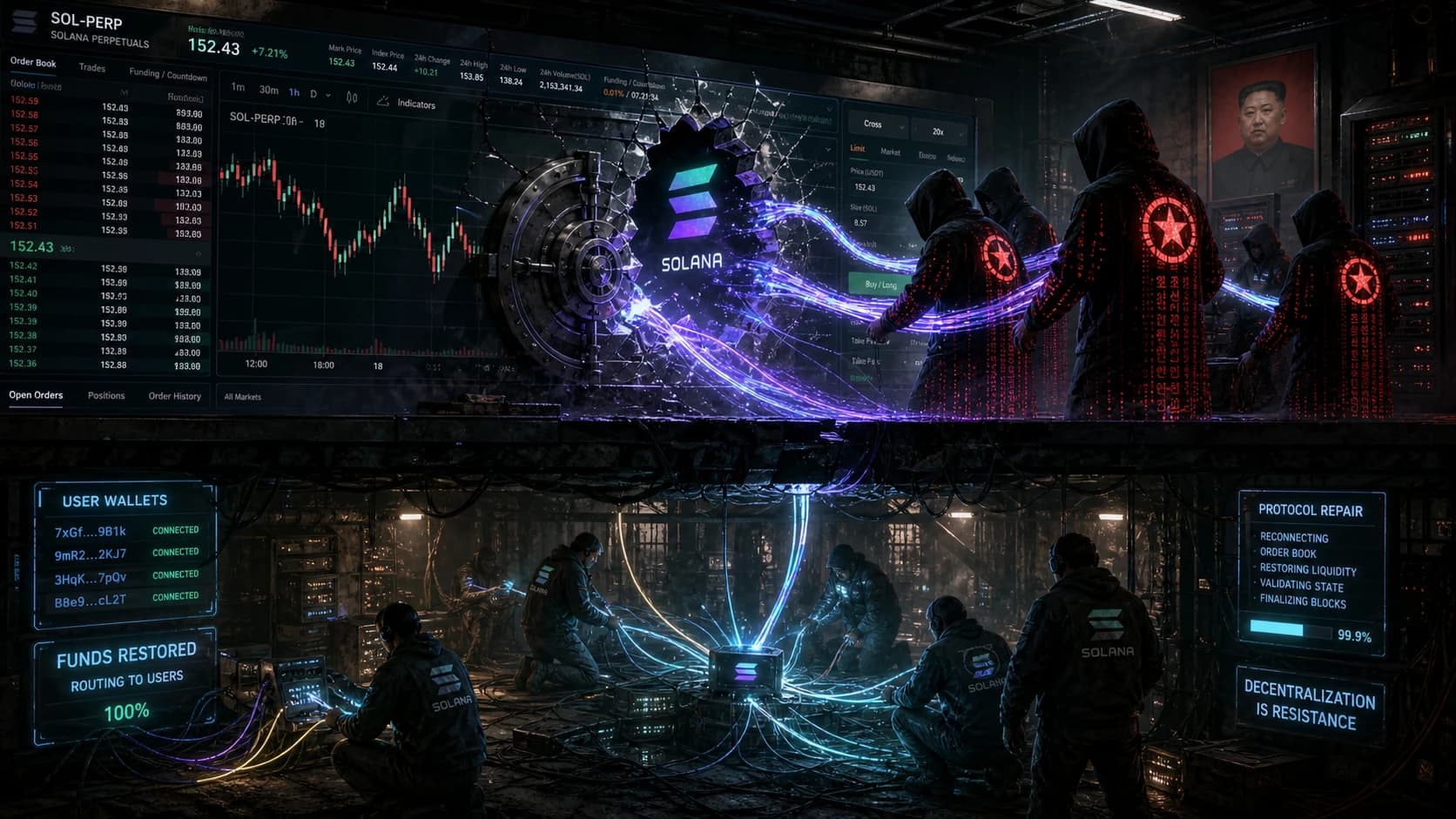
Solana perpetuals exchange Drift has outlined a recovery plan for affected users following a $295 million exploit that blockchain analysts have tied to North Korea-linked threat actors. CoinDesk reported the recovery framework on May 5, 2026, after the protocol published its post-incident steps for depositor reimbursement and risk parameter resets.
The exploit ranks among the largest on-chain attacks of 2026 and lands in a year where DPRK-attributed thefts have already accounted for a sizable share of total stolen crypto. Bitcoin trades at $81,509 (+1.7% over 24 hours) and ETH at $2,373 (+0.5%) as of May 5, 2026, with markets largely shrugging off the Drift news so far. The Fear and Greed Index sits at 50 (Neutral), suggesting the market is treating the exploit as protocol-specific rather than a systemic risk to Solana DeFi.
A $295M hole on a Solana perpetuals venue
Drift is one of Solana's largest derivatives venues, running a hybrid orderbook and on-chain risk engine for perpetual futures. A $295 million loss is meaningful for a Solana-native protocol of its size and is large enough to reshape user trust in Solana perpetuals broadly, not just on Drift itself.
The protocol's recovery plan, as described by CoinDesk, prioritizes depositor reimbursement before any further product expansion. That sequencing matters. After the rsETH drain on Aave earlier this year, DeFi pools committed roughly $300M to make depositors whole, and the speed of that response set a new bar for what affected users now expect from a protocol team after an exploit of this scale.
The DPRK fingerprint
The "DPRK-linked" framing is the part that should grab attention from compliance teams and law firms tracking stolen crypto flows. North Korea-attributed groups, including Lazarus and its sub-units, have been linked to the largest crypto thefts of the past two years, including the Bybit February 2025 incident and the KelpDAO drain. Investigators typically cite consistent on-chain laundering patterns, mixer usage, and address clusters across incidents.
Drift's recovery plan will likely have to coordinate with US Treasury's Office of Foreign Assets Control and other agencies tracing those flows. That introduces friction the team cannot fully control. A separate fight is already playing out around stolen DPRK-linked funds, with Aave currently asking a court to block a $71 million crypto seizure tied to similar attribution claims, and a law firm pulling stolen KelpDAO ETH into a North Korea debt fight. The legal terrain around DPRK-tagged funds is unsettled, and any recovered assets sitting in tagged addresses may end up disputed before they reach Drift users.
This means for Solana DeFi
Solana perpetuals have grown quickly over the past year, with Drift, Jupiter Perps, and several smaller venues taking share from Ethereum L2 derivatives. A $295M security failure on the largest of those venues is a direct test of whether Solana DeFi has matured enough to absorb attacks of this size without a confidence collapse.
Three points worth tracking from here:
- Reimbursement source. Whether Drift covers the loss from treasury, insurance fund, a token-based recovery instrument, or a mix will set the precedent for future Solana DeFi incidents.
- Risk parameter changes. Lending caps, oracle configurations, and circuit breakers usually tighten after an exploit of this size. The post-incident parameters often matter more than the headline reimbursement.
- DPRK fund tracing. If recovered funds sit in OFAC-tagged addresses, US enforcement may claim them before Drift users see anything, similar to the contested seizures already in court for Aave and KelpDAO.
For users with funds on the protocol, the practical step is to read the official recovery plan in full and confirm the claim window and verification process. Recovery programs from prior exploits have typically required sign-in from the affected wallet within a defined window and have not made later claims easy.
Overview
Drift published a recovery plan for users after a $295 million exploit on its Solana perpetuals platform that on-chain analysts have linked to DPRK threat actors. The plan prioritizes depositor reimbursement, but DPRK-tagged funds raise enforcement complications that have already created legal disputes for other protocols. Solana DeFi's response to this incident will set the bar for how the ecosystem handles eight-figure losses going forward.