Cantina's autonomous security tool Apex flagged a signature-validation bypass in the XRP Ledger's proposed Batch amendment on February 19, 2026, eight days before the XRPL Foundation publicly disclosed the flaw. Had the amendment activated on mainnet before the catch, attackers could have executed transactions from any account on the ledger without possessing the victim's private keys, putting as much as $80 billion in XRP market capitalization at direct risk, as of the time of disclosure.
No human auditor found it first. The AI did.
A Loop Error That Would Have Bypassed Every Signature Check
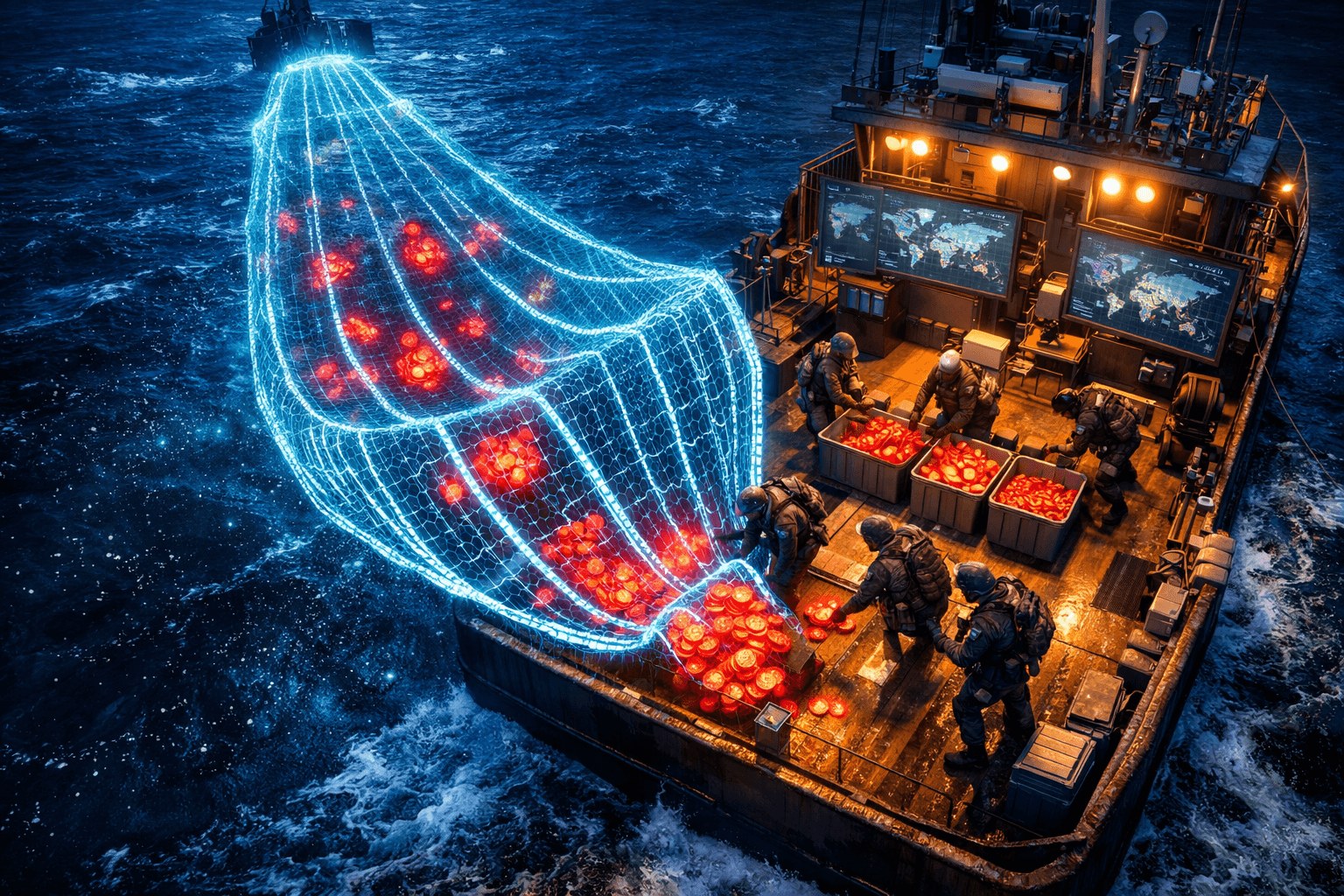
The Batch amendment, tracked as XLS-56, was designed to let users group multiple "inner" transactions into a single outer batch. To save processing power, those inner transactions were intentionally left unsigned, with authorization delegated to the outer batch's signer list.
The problem sat in the validation loop. If the system encountered a signer for an account that did not yet exist on the ledger, and the signing key matched that nonexistent account, it immediately declared the validation a success and exited the loop. No further checks ran. The remaining signers in the list were never evaluated.
That early exit turned the entire signature model into a rubber stamp. An attacker could sequence specific batched transactions to exploit the premature validation, authorizing fund transfers, ledger state modifications, and effectively draining wallets at will.
The amendment was in its voting phase among XRPL's Unique Node List validators when Cantina's Apex bot caught the flaw through static analysis of the rippled codebase. It had not yet activated on mainnet. No user funds were ever at risk.
$80 Billion and the "Largest Hack That Never Happened"
Hari Mulackal, CEO of both Cantina and Spearbit, did not hedge when describing the potential impact. "Had this been exploited, it would have been the largest security hack by dollar value in the world, with nearly $80 billion at direct risk," he stated. That figure reflects XRP's total market capitalization at the time of disclosure. While not every token would have been drained in practice, the signature bypass was universal: any account on the ledger could have been compromised.
For context, the largest confirmed crypto exploit remains the Ronin Bridge hack in March 2022, which drained $625 million. The Poly Network hack took $611 million. The XRPL vulnerability, if exploited before detection, would have dwarfed both by two orders of magnitude.
The distinction matters because this was not a smart contract bug on a niche DeFi protocol. It was a consensus-level flaw in the core signature validation of a top-ten blockchain by market capitalization. The blast radius would have extended to every wallet, every DEX order book, and every application built on XRPL.
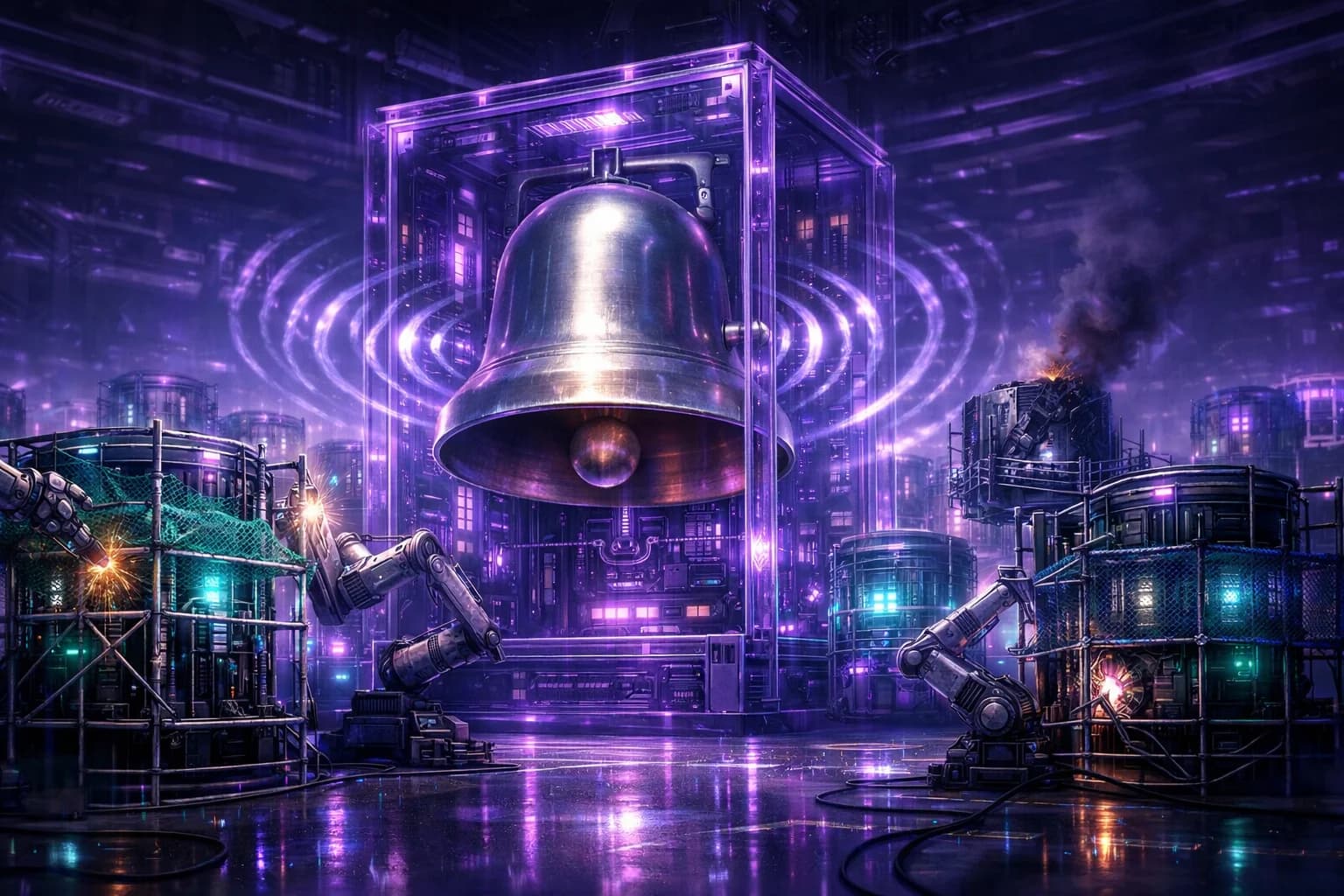
The Four-Day Emergency Patch
The timeline moved fast once the disclosure reached Ripple's engineering team:
- February 19: Pranamya Keshkamat, a security engineer at Cantina, and the Apex AI bot identify the flaw through static analysis.
- February 19 (same day): Responsible disclosure to Ripple's engineering team, who validate the report.
- Immediately after: XRPL Foundation advises all Unique Node List validators to vote against the Batch amendment's activation.
- February 23: Emergency release of rippled 3.1.1 ships. The update marks both the Batch amendment and a related amendment, fixBatchInnerSigs, as unsupported, blocking them from activating on the network.
- February 27: Public disclosure.
Four days from discovery to patch. Eight days from discovery to public announcement. In blockchain security, where governance votes can take weeks and social coordination among validators is notoriously slow, that response time is notable.
A corrected replacement amendment, BatchV1_1, has been implemented and is currently undergoing review. The revised version removes the early-exit loop, adds authorization guards, and tightens the scope of the signing check.
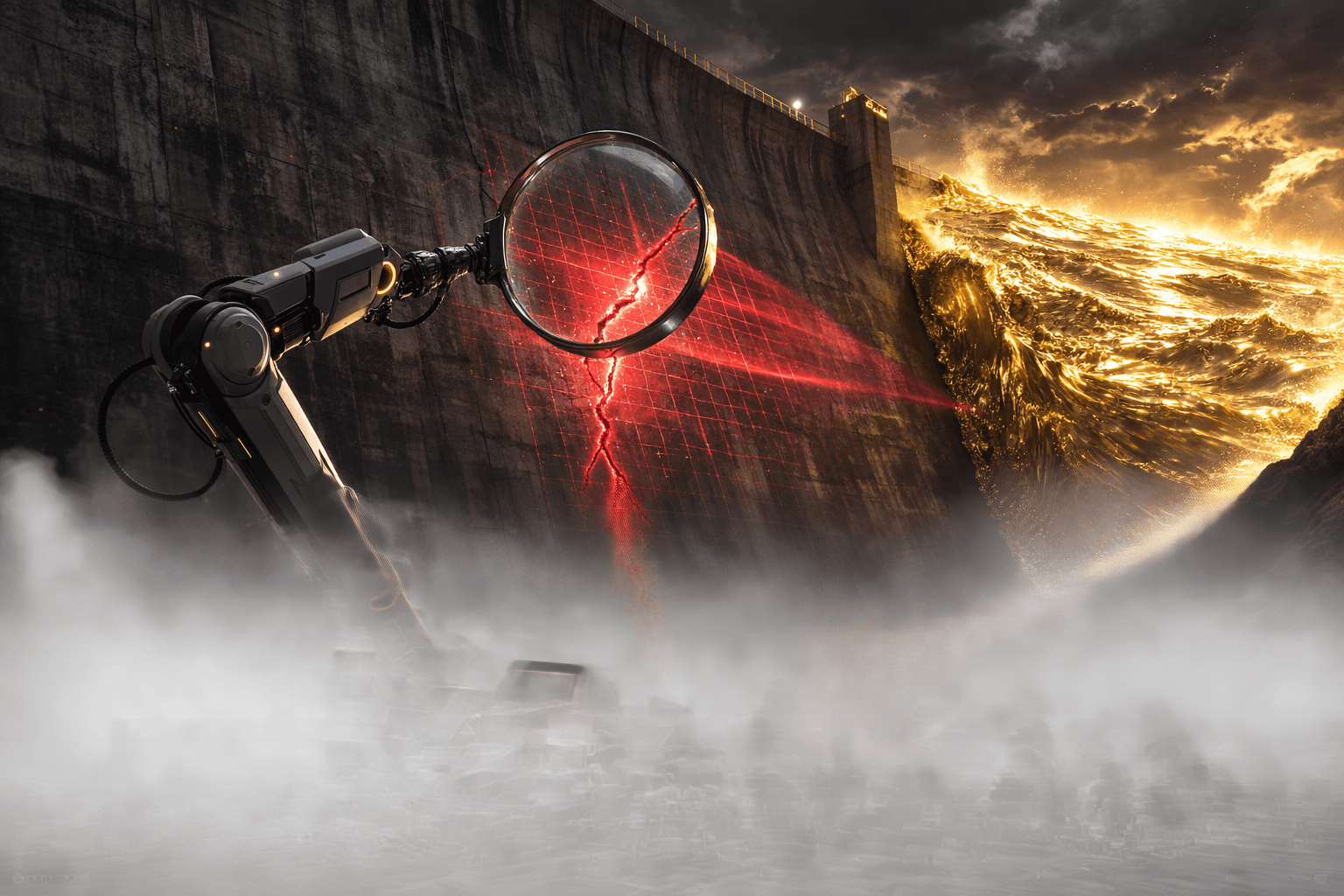
What This Means for AI in Blockchain Security
The XRPL incident is not the first time an AI tool has found a blockchain vulnerability, but it is the highest-stakes catch to date. Apex operates as an autonomous bug hunter using static code analysis, scanning codebases for logic flaws that traditional testing might miss. The signature-validation bypass was a logic error, not a memory corruption or overflow. It required understanding the intended behavior of the signer loop and recognizing that a specific edge case (nonexistent account with a matching key) would short-circuit the entire validation chain.
This is the category of bug that human auditors routinely miss because the code compiles, the unit tests pass, and the happy path works correctly. The vulnerability only surfaces when an adversary deliberately constructs a batch transaction targeting the edge case. Static analysis tools, particularly AI-driven ones trained on vulnerability patterns across multiple codebases, are increasingly effective at catching exactly these logic errors.
For the broader crypto ecosystem, the takeaway is straightforward. AI-augmented security auditing is no longer a nice-to-have. When an $80 billion network nearly shipped a consensus-level signature bypass to mainnet, and an AI caught it before any human did, the argument for autonomous security tooling writes itself.
The Ripple Effect on XRP and the Ledger's Reputation
XRP traded at approximately $1.41 at the time of the announcement, down 2.33% over 24 hours, with limited price reaction. Markets appeared to treat the story as a near-miss rather than an active threat, which is technically correct: the amendment never activated, and no funds were lost.
But the reputational implications run deeper. XRPL positions itself as an institutional-grade ledger for payments, cross-border settlement, and increasingly, tokenized real-world assets. A signature bypass reaching the voting stage, even if caught before activation, raises questions about the code review process that allowed it to get that far.
The XRPL Foundation acknowledged as much, stating that the vulnerability "could have destabilized a large-scale exploitation ecosystem and led to a loss of trust in XRPL." The corrective measures, including the BatchV1_1 replacement with stricter authorization guards, suggest the foundation is treating this as a process failure, not just a code bug.
For users holding XRP or using XRPL-based applications, the practical risk is now zero. The amendment is blocked, the patched version is in review, and validators were advised to reject activation. But the incident reinforces a recurring lesson in crypto: self-custody and vigilant security practices remain the best defense against systemic risk, regardless of which chain you are on.
Overview
Cantina's AI security bot Apex discovered a critical signature-validation bypass in the XRP Ledger's proposed Batch amendment on February 19, 2026. The flaw would have allowed attackers to drain any wallet on the ledger without needing the victim's private keys, putting up to $80 billion at theoretical risk. No human auditor caught it first. The XRPL Foundation issued an emergency patch (rippled 3.1.1) within four days, blocking the amendment from activating on mainnet. No funds were lost. A corrected replacement, BatchV1_1, is now in review. The incident marks the highest-stakes blockchain vulnerability ever caught by an AI tool and accelerates the case for autonomous security auditing across the industry.