Charles Guillemet does not think the security situation in crypto is getting better. The Ledger CTO told CoinDesk on April 5 that artificial intelligence is collapsing the cost and time required to attack crypto protocols, and the industry is not adapting fast enough to keep up.
"The cost of cyberattacks is going down to zero," Guillemet said. Tasks that once demanded months of skilled reverse engineering, finding vulnerabilities, and chaining exploits together can now be done "in seconds" with AI tooling.
$1.4 Billion Gone, and the Tools Are Getting Cheaper
The numbers back the warning. Crypto losses from attacks have reached $1.4 billion over the past year. Two of the most severe came in rapid succession: the Drift Protocol exploit drained $285 million from the Solana-based perpetuals platform this week, and the Resolv protocol attack cost $25 million the week before.
What makes the current moment different from previous exploit cycles is the tooling. AI does not just help attackers find vulnerabilities faster. It helps them chain multiple weaknesses together, generate malicious code at scale, and scan compromised devices for wallet seed phrases, all with less expertise than ever required. The barrier to entry for sophisticated crypto attacks is falling while the attack surface keeps expanding.
BTC was trading at $66,883 as of April 5, 2026, down 0.5% over 24 hours, with the Fear and Greed index sitting at 29 (Fear). The broader market mood already reflects unease, and a structural decline in exploit costs adds another layer.
Why Audits Alone Are Not Enough Anymore
Guillemet's core argument is that traditional security audits, the standard defense for most DeFi protocols, cannot keep pace with AI-augmented attack methods. An audit is a point-in-time review. AI lets attackers probe continuously.
His alternative: formal verification. Instead of human reviewers reading code and looking for bugs, formal verification uses mathematical proofs to validate that code behaves exactly as intended under all possible conditions. It is slower and more expensive to implement, but it eliminates entire classes of vulnerabilities rather than catching them one at a time.
"There is no 'make it secure' button," Guillemet said. Protocol teams need to "be perfect" in their development, a standard that becomes harder to meet as AI-generated code spreads across the ecosystem. When one vulnerable code pattern propagates through multiple protocols via AI-assisted development, a single flaw can cascade.
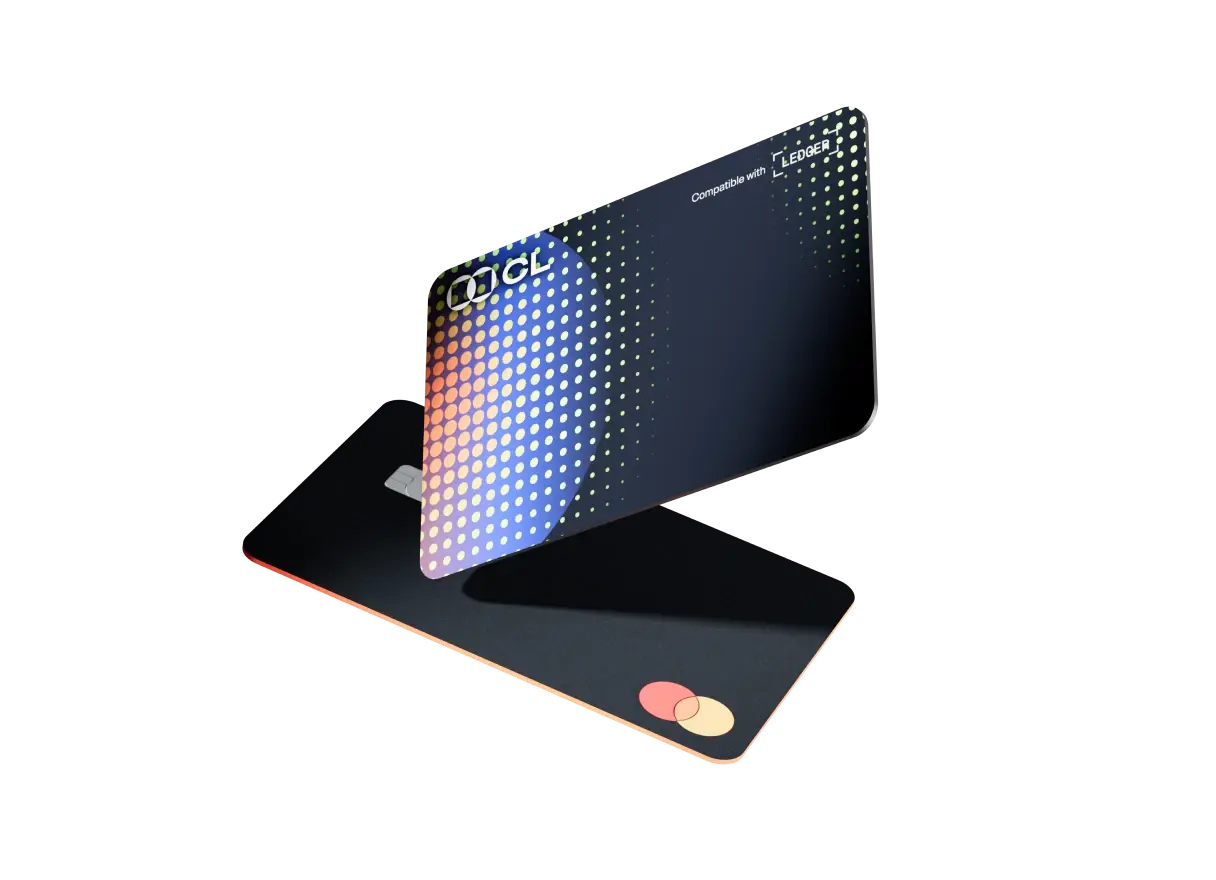
Hardware Isolation as the Last Line
For individual users, Guillemet pointed to hardware-based security as the most reliable defense. Keeping private keys on a device that never connects to the internet removes the largest attack vector: remote access. Self-custody wallets that isolate keys in secure hardware elements remain resistant to AI-driven software exploits because the attack surface is physically separated.
The logic extends beyond wallets. Advanced malware now scans compromised phones for seed phrases stored in notes apps, screenshots, or clipboard history. Cold storage and disciplined offline key management are the user-side equivalent of what formal verification does for protocols: they reduce the problem space rather than trying to patch every possible hole.
Cards built on self-custody architecture inherit this advantage. Ledger's CL Card, for example, keeps keys on the hardware device while enabling spending, a design that sidesteps the software-layer vulnerabilities Guillemet described.
The Divide Ahead
Guillemet expects the industry to split. Critical systems, exchanges, custodians, and protocols holding billions, will invest heavily in formal verification, hardware security modules, and AI-specific defenses. The rest of the software ecosystem may not keep pace.
That split has real consequences for users choosing where to hold and spend crypto. A protocol with a clean audit from 2025 is not necessarily safe in 2026 if it has not adapted its security posture to AI-era threats. The Drift exploit, attributed to a six-month North Korean intelligence operation, showed that even well-audited protocols can fall to patient, well-resourced attackers. AI lowers the resource threshold.
Users should assume systems can and will fail, Guillemet said. That means not keeping all funds on any single protocol, using hardware wallets for long-term storage, and treating every connected device as a potential attack surface.
Overview
Ledger CTO Charles Guillemet warned that AI is compressing the cost and time of crypto attacks toward zero, with $1.4 billion lost over the past year. He called for formal verification over traditional audits, hardware-based key isolation, and the assumption that any connected system will eventually be compromised. The Drift Protocol and Resolv exploits illustrate the scale of current threats, and AI tooling is making them cheaper to execute.