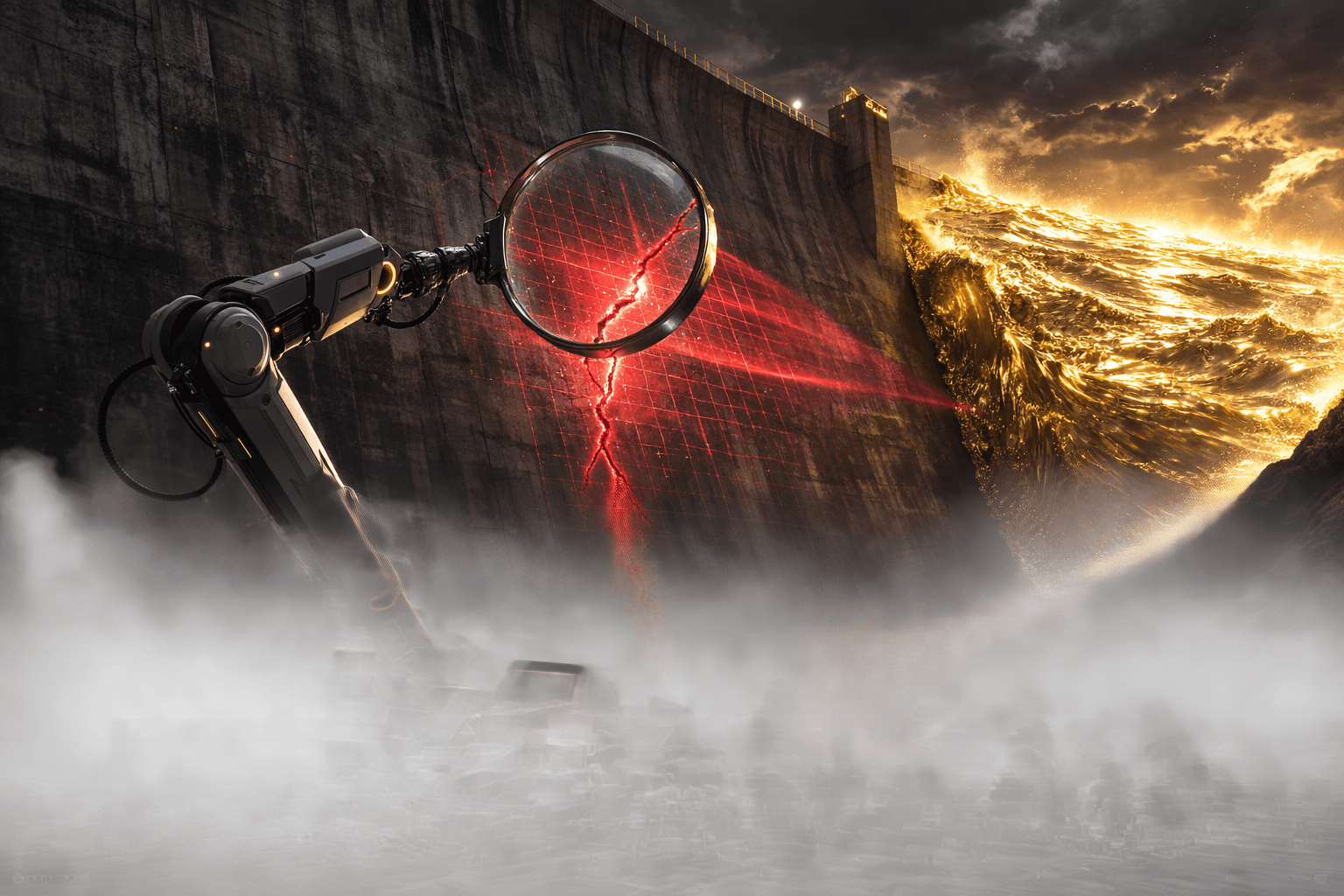
Google's Threat Intelligence Group has published its findings on Coruna, a previously unknown iOS exploit kit that chains together 23 separate exploits across five attack sequences to compromise iPhones running iOS 13.0 through 17.2.1. The kit, as of March 5, 2026, has been observed stealing cryptocurrency wallet data from apps including MetaMask, Bitget Wallet, Base, and Exodus, and it can decode seed phrase QR codes stored in a device's photo library.
The discovery marks what mobile security firm iVerify calls "the first observed mass exploitation against iOS devices," a shift from the kind of surgical, one-target-at-a-time attacks that iPhone spyware has historically been known for.
Five Exploit Chains, Three Threat Actors, One Kit
Coruna is not a single vulnerability. It is a modular framework containing five complete exploit chains built from 23 individual exploits, including several that were once zero-days. The kit fingerprints incoming devices with JavaScript, identifies the iPhone model and iOS version, then selects the appropriate WebKit remote code execution exploit and pairs it with a pointer authentication code (PAC) bypass to escape the browser sandbox.
The CVEs read like a greatest-hits list of iOS security research from the past three years:
- CVE-2024-23222: A WebKit type confusion flaw affecting iOS 16.6 through 17.2.1, originally exploited as a zero-day before Apple patched it in early 2024
- CVE-2023-43000: A WebKit use-after-free bug covering iOS 16.2 through 16.5.1
- CVE-2023-32434 and CVE-2023-38606: The "Photon" and "Gallium" exploits previously weaponized in Operation Triangulation, the campaign Kaspersky discovered targeting its own employees in 2023
- CVE-2022-48503: A WebKit flaw added to CISA's Known Exploited Vulnerabilities catalog in October 2025
Two of those exploits were originally part of Operation Triangulation, which means code from one of the most sophisticated iOS attack campaigns ever documented has now found its way into a financially motivated crime toolkit.
From Surveillance Vendor to Russian Spies to Chinese Crypto Scammers
Google tracked Coruna across three distinct phases, each escalating in scale and lowering in sophistication of the operator.
In February 2025, the kit appeared in a "highly targeted" operation conducted by a customer of a commercial surveillance vendor. Google did not name the vendor. This was precision work: specific individuals, specific devices, no collateral exposure.
By July 2025, the framework surfaced on compromised Ukrainian websites, including industrial equipment retailers and e-commerce platforms. Google attributes this phase to UNC6353, a suspected Russian espionage group that selectively targeted iPhone users based on geography.
Then in December 2025, the kit showed up on a sprawling network of fake Chinese websites themed around finance and cryptocurrency, including at least one site spoofing the crypto exchange WEEX. This time there was no geographic filtering. Anyone visiting the page on a vulnerable iPhone got hit. Google attributes this phase to UNC6691, a financially motivated threat cluster likely operating from China.
The progression matters: a tool built for intelligence agencies is now being used for mass financial crime.
How PlasmaLoader Hunts for Seed Phrases
The final payload deployed by UNC6691 is a stager binary called PlasmaLoader (internally tracked as PLASMAGRID). Once the exploit chain achieves root-level access, PlasmaLoader injects itself into powerd, a system-level iOS daemon that manages power state, giving it persistence that survives app closures.
From there, PlasmaLoader does three things:
- Wallet extraction: It pulls data from cryptocurrency apps including MetaMask, Bitget Wallet, Base, and Exodus, targeting stored keys and session tokens
- QR code scanning: It decodes QR codes from images stored on the device, hunting for seed phrase backups that users photograph for convenience
- Keyword search: It scans text messages, notes, and clipboard history for strings like "backup phrase," "recovery phrase," and "bank account"
The binary phones home to hardcoded command-and-control servers, with a fallback domain generation algorithm seeded with the string "lazarus" that produces 15-character domains on the .xyz TLD. It validates those domains through Google's own public DNS before establishing a connection.
Who Is Actually at Risk
The exploit kit targets iPhones running iOS 13.0 through 17.2.1, which means any device released between September 2019 and December 2023 that has not been updated. Apple's current release is iOS 18.x, so anyone on the latest software is not affected.
But "just update" is not as simple as it sounds. Older devices like the iPhone 8 and iPhone X cannot run iOS 18 at all. Users on those devices are permanently vulnerable to at least some of Coruna's exploit chains unless they enable Lockdown Mode, which Google confirmed will prevent execution. Private browsing mode in Safari also blocks the kit, as Coruna performs environment checks and skips execution under defensive configurations.
The watering hole delivery method, where the user simply visits a compromised webpage with no additional clicks required, makes this particularly dangerous. There is no phishing email to spot, no suspicious attachment to avoid. The fake crypto sites look legitimate, and the exploit fires silently through a hidden iFrame.
What Crypto Users Should Do Right Now
The practical defense checklist is short:
Update your iPhone. If you are running anything below iOS 18, update immediately. This single action neutralizes all five of Coruna's exploit chains.
Enable Lockdown Mode. If your device cannot run iOS 18 (iPhone X or older), go to Settings, then Privacy and Security, then Lockdown Mode. This disables the WebKit features that Coruna exploits.
Stop photographing seed phrases. PlasmaLoader's QR code scanner targets exactly this behavior. If you have photos of seed phrases or recovery cards in your camera roll, delete them and store backups offline on paper or metal.
Use self-custody wallets with hardware signing. A compromised phone cannot steal keys that never touch the device. Hardware wallets like Ledger keep signing keys on a separate chip.
Audit your browser history. If you have visited unfamiliar crypto or finance sites on an older iPhone in recent months, consider your wallet credentials potentially compromised and rotate them.
The Bigger Picture: Spyware Trickle-Down Is Accelerating
The Coruna story fits a pattern that the security community has been warning about for years. Tools developed for or by surveillance vendors, priced in the millions and sold to government clients, eventually leak into the hands of nation-state actors and then into financially motivated criminal operations.
iVerify's assessment is blunt: "Coruna is one of the most significant examples we've observed of sophisticated spyware-grade capabilities proliferating from commercial surveillance vendors into the hands of nation-state actors and ultimately mass-scale criminal operations."
For crypto users specifically, this means the threat model has changed. The attackers targeting your MetaMask wallet are no longer just phishing operators with cloned websites. They now have access to zero-day exploit chains that can compromise your device through a single page visit, no interaction required.
The silver lining, if there is one, is that Apple's newer iOS versions have closed these attack surfaces. But the window of vulnerability, four years of iOS versions across hundreds of millions of devices, is enormous.
FAQ
Does Coruna affect the latest iPhones? No. The exploit kit targets iOS 13.0 through 17.2.1. Devices running iOS 18 or later are not affected by any of the five exploit chains.
Can Coruna steal crypto from a hardware wallet? No. Coruna targets software wallets installed on the iPhone itself. Hardware wallets that keep private keys on a separate device are not vulnerable to this attack.
How do I know if my iPhone was compromised? There is no simple user-facing indicator. If you visited unfamiliar crypto or finance websites on an older iPhone, assume potential compromise and rotate your wallet credentials. iVerify offers a mobile threat detection tool that can scan for indicators of Coruna infection.
Is this related to NSO Group's Pegasus? Google did not attribute Coruna to NSO Group. However, the exploit reuses code from Operation Triangulation (discovered by Kaspersky in 2023), and iVerify has suggested possible links to US-developed surveillance tools, a claim Kaspersky has disputed.
Overview
Google's Threat Intelligence Group has exposed Coruna, a modular iOS exploit kit containing 23 exploits across five attack chains that targets iPhones running iOS 13.0 through 17.2.1. Originally used by surveillance vendors and Russian espionage groups, the kit was repurposed by a Chinese financially motivated threat actor (UNC6691) to steal cryptocurrency wallet data from MetaMask, Bitget Wallet, Base, and Exodus through fake finance websites. The payload, PlasmaLoader, can extract wallet keys, decode seed phrase QR codes from photos, and search device text for recovery phrases. Users should update to iOS 18, enable Lockdown Mode on older devices, and never store seed phrases as photographs.
Recommended Reading
- What Happens in the 2 Seconds After You Tap a Crypto Card
- Solflare Launches PAL: The First Wallet-Native Privacy Aggregator on Solana
- ZachXBT Exposes Axiom Employees Allegedly Abusing Internal Tools to Track User Wallets and Insider Trade